Internet
How to delete my information from the Internet

The Internet is one of the best tools of the 21st century. With his arrival, the digital revolution began, which has helped us evolve and transform our way of communicating and relating. However, with the development of the Internet, our exposure has also grown, since day after day we use social networks, forums, blogs or fill in multiple online forms to, for example, reserve tickets or subscribe to a publication.
All of this makes us vulnerable users who share their personal data on a daily basis. Do you want to know how to delete your information from the Internet?
The use of personal data on the Internet
The Internet is a powerful tool that we make daily use of. It has changed our way of relating and communicating, it has transformed the markets and has contributed to improving our day-to-day life. However, it also has its cons.
Every day we provide the network with a large amount of personal information, much more than we can imagine, which is stored little by little and can be exposed or be available to anyone at any time.
In addition to social networks, blogs or forums, many are the pages that require us to include our personal data to register or subscribe to it. Have you thought about how many times have you added your personal information on the Internet, whether to buy, access an online site or download a document? If you stop to think about how many times you expose your personal data, you will realize that this information is freely browsing the net and may be available to many. You can see how easy it is to get personal data from others in this other article on How to get a person’s data.
Our relationship with the network is close, daily and continuous. Therefore, it is important to reflect on how we relate to it, in order to minimize our exposure and protect our privacy.

How to delete personal information from the Internet
Surely on more than one occasion, you have asked yourself: can my personal information be deleted from Google? The answer is yes: it is possible to make your personal data disappear from the Internet, although it is a task that takes time and work.
Find Google’s activity controls here
Address, telephone, full name, account number … These are some of the most sensitive data that should not circulate freely on the Internet, since anyone could access it. To guarantee your peace of mind, in addition to having professional services, you can follow some steps so that the most relevant personal information about you can disappear from the network, such as those that we will explain below.
Delete my personal information from the Internet from search engines
The first step to delete your data from the Internet is to do it directly from the search engines that you use the most. Google, Bing or Yahoo, among others, have, among their tools, the possibility of erasing personal information. These online search engines allow you to get rid of such data as long as the requirements established by these companies are met, however, they guarantee the privacy rights of users.
Likewise, there are court rulings that oblige these search engines to eliminate the search results if their users request it, provided that the circumstances support it.
How to erase my social media trail
Currently, social networks are the channel with the greatest personal exposure by users, and controlling them is not an easy task. If you do not want to have a presence on the web, you should deactivate or eliminate all social networks, so that the search engines would not index them in the first place.
If what you want is to delete specific content, the safest way is to do it through the attention to the user of each application. Facebook, Twitter, Instagram, Pinterest, Youtube or LinkedIn are some of the most used by Internet users and, therefore, the ones that most expose your personal data.

How to delete my personal data from other websites
If having deleted the search engine results, you still feel that there is personal data exposed on the Internet, the next step will be to remove this information from any website. You can do this by contacting the site or company that has your data and requesting them to delete it within a period of up to 10 days by law.
Likewise, you can unsubscribe from subscriptions or newsletters whenever you want or access these services as long as the company guarantees to comply with the data protection law.
In the event that you do not remember if you have created an account or have registered on a website, you can track your information online to locate it and, thus, be able to eliminate it. The procedure is simple: write your name or your email in any search engine, using quotation marks, and among its results, you will see all the sites that contain important or relevant information about you.
Companies that erase data from the Internet
If you want to make sure that all your personal data has disappeared from the Internet, do not hesitate to contact professionals and specialists. Among the services they offer you, the following stand out:
- Deletion of personal information
- Clear Google data either personal or brand
- Delete data from social networks and forums
- Reach agreements with the media if they favor a bad reputation for your person, company or brand.
Comments, videos, photographs, personal information in the media, eliminating your name from search engines … Eliminating your trace on the Internet is possible if you have the best specialists.
Internet
Transform Your Text with Fancy Fonts: A Dive into Online Font Generator Websites
In today’s digital age, expressing ourselves creatively is more important than ever. One fun and engaging way to do this is by using fancy fonts to enhance the appearance of our text. If you’re looking to add a touch of uniqueness to your social media posts, captions, or any other written content, you’re in luck! Several websites offer free and user-friendly fancy font generators that can instantly transform your plain text into eye-catching designs. In this article, we’ll explore some of the top fancy font generator sites that can help you stand out in the online crowd.
1. Aesthetic-Symbol.com
Text symbols have evolved into a new form of visual communication, allowing individuals to convey emotions, concepts, and ideas with a single character. Aesthetic-Symbol.com takes this concept to the next level by curating an extensive collection of symbols that resonate with various themes and moods.
- Social Media Magic: Elevate your social media game by using these symbols to enhance your captions, comments, and bios. Express emotions, add emphasis, or even create stylish dividers between sections of your content.
- Text Messages with a Twist: Surprise your friends with creatively designed symbols that add a touch of novelty to your text messages. Birthdays, celebrations, or just a friendly “hello” – there’s a symbol for every occasion.
- Personal Branding: In the digital era, personal branding matters. Aesthetic-Symbol.com allows influencers, bloggers, and professionals to incorporate unique symbols into their branding materials, making their content instantly recognizable.
- Artistic Endeavors: Creative minds can use these symbols to enhance digital artwork, presentations, and graphics. With a wide range of choices, the possibilities are limited only by imagination.
2. LetrasparaNick.com and Letrasdiferentesparanick.com
If you’re active on platforms like Instagram, TikTok, or Twitter, you know the importance of a captivating username or nickname. LetrasparaNick.com and Letrasdiferentesparanick.com specialize in generating unique fonts that you can use to make your username pop. From fancy script fonts to creative symbols, these websites make it easy to customize your online identity.
3. Fuentesletras.com and Fontesparainstagram.com
Fuentesletras.com and Fontesparainstagram.com cater to those looking for fonts tailored for Instagram. With the visual-centric nature of this platform, having fonts that stand out is crucial. These websites offer a range of fonts that suit different moods and themes, helping you make your posts and stories more visually appealing.
4. ConvertidordeLetras.com and Fontesparaig.com
ConvertidordeLetras.com and Fontesparaig.com are versatile fancy font generator sites that provide fonts suitable for various purposes. Whether you’re crafting an email signature, designing a poster, or creating unique graphics for your blog, these websites offer a plethora of font options to choose from.
5. Letrasgoticas.com and Conversoresdeletras.com
Letrasgoticas.com and Conversoresdeletras.com can make different styles of fonts that look cool. You can use these fonts for lots of things like making an email signature, designing a poster, or creating special pictures for your blog. These websites have many font options to pick from.
Conclusion
Expressing your individuality and creativity through your text has never been easier, thanks to the plethora of fancy font generator sites available online. Whether you’re looking to add a touch of elegance, playfulness, or uniqueness to your text, these websites have the tools you need. Websites like Aesthetic-Symbol.com, LetrasparaNick.com, Letrasdiferentesparanick.com, FontesLetras.com, Fontesparainstagram.com, ConvertidordeLetras.com, and Fontesparaig.com are just a few examples of the many resources at your disposal. So go ahead and explore these platforms to transform your ordinary text into something extraordinary!
Internet
How To Fix Temporarily Lost Connection
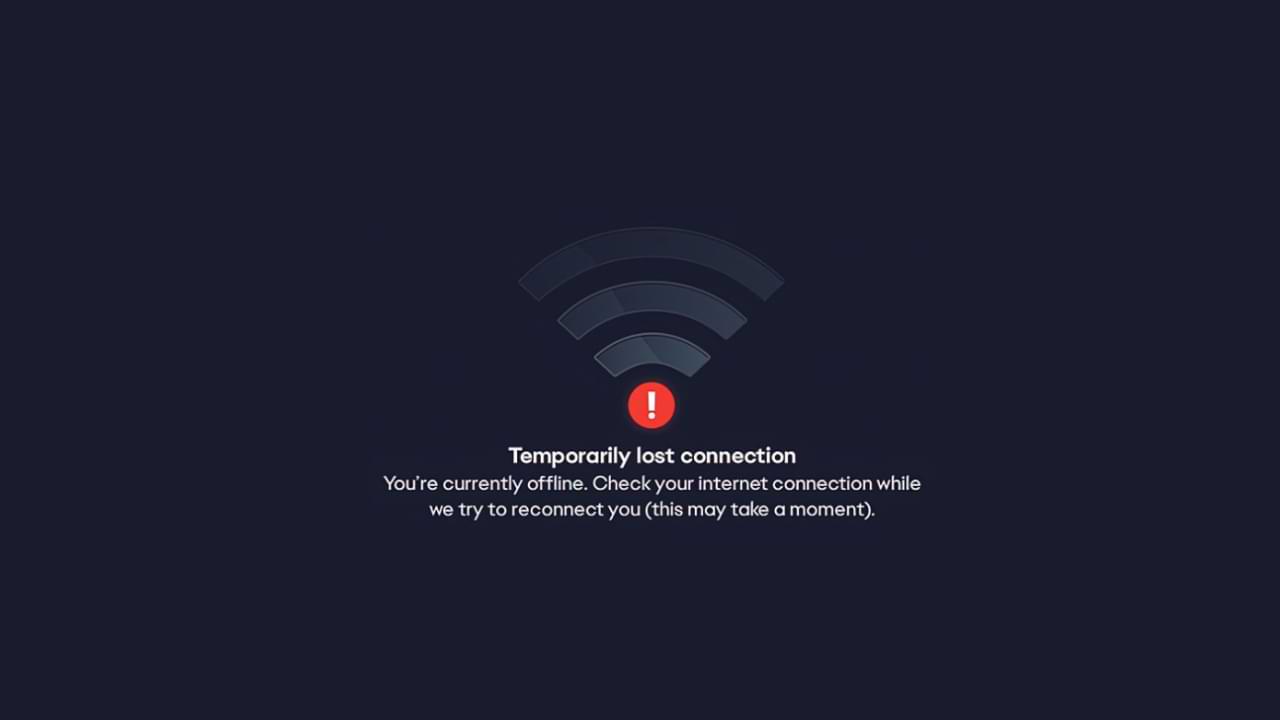
The temporarily lost connection problem is a Temporarily Lost Connection error when launching the EA application. There are quite a number of games made by EA that cannot be played due to the appearance of this error.
It looks like this problem is on the EA side, so there’s not much you can do to fix it, but there are a few tips you can do.
However, we have some suggestions that can help solve the problem. How to fix EA temporarily lost connection error Usually caused by EA server connectivity.
Some things you can do to overcome this are:
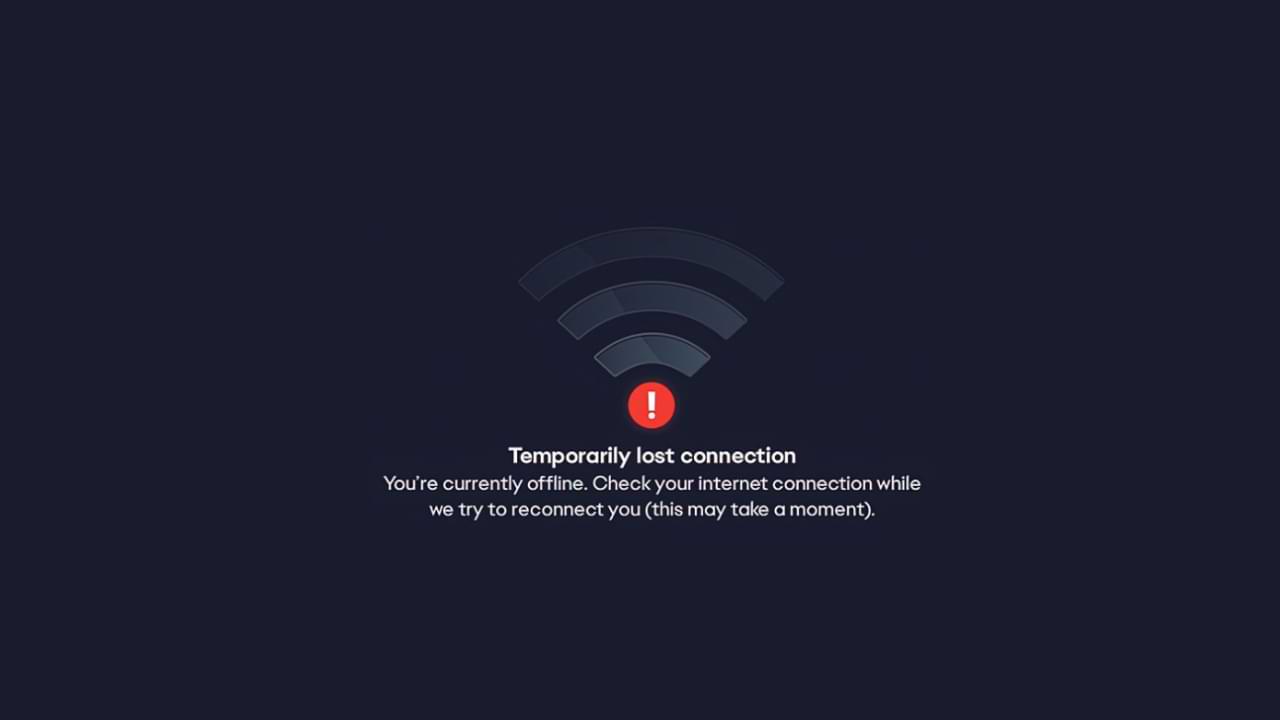
- The first step, make sure to link your Steam and EA accounts.
- Then, run the EA application as an administrator.
- Restart your PC/Laptop
- Also, restart your router and modem.
- Uninstall the EA app and reinstall it.
- Ensure that EA applications are allowed through your firewall and anti-virus software.
- Finally, check if your router is blocking the connection to the EA server.
These are common fixes you can make. If, in the above way the error still appears. We can confirm that the cause of the problem is not on you. However, there is a problem with the EA Server. The best solution for this is to wait a while, as usually, problems like this don’t last that long.
Internet
How to Solve WiFi Authentication Problem
If you open WIFI at a school, cafe, airport, or hotel, you are usually asked to enter username and password login information first. Usually, this login information will be given to you beforehand.
Maybe you have or are currently experiencing a problem where there is no login display at all when accessing wifi. Then this article will help you to overcome it.
Here is a solution to overcome Wifi that can’t log in:
1. Restart your Device
This solution is easy solution and can be done by anyone.
What you need to do is:
- Disconnect from the network and turn off your Wi-Fi.
- Log out of the user account on your computer and shut down the system.
- Restart the device and log back into your user account.
- Turn on your Wi-Fi and connect to the network once again. See if the login page will now appear in your browser.
2. Use Public DNS
The next method is to use public DNS, how to set it up, follow these steps:
- To change a Wi-Fi network, go to Settings menu > Network Settings. Select the Wi-Fi network you want to change the DNS for, long press on the network name, and select ‘Modify Network ‘
- Then in the “ IP Settings” option. Usually, it will read ‘DHCP‘. Change it to ‘Static’, and you will be able to input the DNS IP manually you will use.
- Then enter DNS 8.8.8.8 and 8.8.4.4
3. Use a VPN App to solve the WIFI Login problem
When you join a WiFi hotspot with a login page, the VPN app will display information asking if you want to log in.
4. Forget the WIFI Network and Reconnect
Go to your device Settings and tap on WiFi > Find a network that you are having trouble connecting to a WiFi network > Long press on the network either SSID /Network Name, then you will see a small window with options to forget the network or modify network configuration. You can simply Tap on Forget Network option and then reconnect.
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone