How-To
Security tips for public Wi-Fi networks

Today there are many public places that offer free Wi-Fi connections, such as trains, shopping centers, stations, or cafes. We explain the dangers of using them and how you should protect yourself.
The free Wi-Fi connections that you can find in public places offer us a practical way to connect to the network without having to consume data from our operator’s data plan. Sometimes it is the only alternative for your laptop or tablet.
However, these public Wi-Fi connections are not at all secure. Here we explain why, and also how you should proceed to make everything more secure and not expose your device and your data to hackers.
Many coffee shops seem to have become the open offices of the 21st century. Even before the COVID-19 coronavirus crisis, it was easy to visit any Starbucks store and come across a sea of users with laptops or iPads.
Now, although many try to seek some privacy in the work they are carrying out, the truth is that the Wi-Fi connection in a public place like the one they are using is not secure and will be exposing them to other types of dangers.
Why is public Wi-Fi not secure?
The free Wi-Fi connection has a hidden cost and is called security. While we like the idea of being able to roam around a city by connecting to multiple Wi-Fi hotspots at no cost, this is certainly dangerous, as most of these networks are not encrypted.
In order to facilitate connections and avoid administration or supervision, these access points generally do not require a password to connect. When you connect, a web page appears asking you to enter an email address.
The problem with this is that the connection between your device and the access point is not encrypted. Therefore, some data will be sent in the form of plain text, which means that anyone could spy on your actions.
Worse still, they could set up their own access point and call it something like “Starbucks wifi.” Then people will connect to it without hesitation, giving the criminal easy access to all your unencrypted data or relevant information from you.
What are the dangers of using free wifi?
These fake networks look real and allow you to access the Internet as you normally would, but all they do is spy on you. Sooner or later, they will ask you to download something innocent looking that will contain malware to take over.
Another danger is that the Wi-Fi provider you connect to does not securely store the data that you used when registering. Sometimes these servers store the information on an Amazon server without a password, exposing everything to anyone.

Please note that when you log into any network, the device will store those details so that you can automatically connect again when you are within range of the network or come back another day.
For trusted networks like those in your home or office, this is fine. But when you do it from anywhere, this can turn against you. The fake network can impersonate another network to get the relevant information from your phone or device.
How can I make the public Wi-Fi connection secure?
The answer seems obvious: using a VPN connection.
A virtual private network (VPN) creates an encrypted connection between your device and a secure network server. If this sounds complicated, it really is not. Just install the VPN app and then enter your login details
Almost all VPN apps have a quick connect button that selects the closest or fastest server and it only takes a few seconds to connect.
The best apps have an option in the settings to automatically connect whenever your phone connects to public (unsecured) Wi-Fi, so you’re protected even if you forget to enable the VPN.
There are many providers and a wide variety of options, but you will find a comprehensive buying guide for this year’s best VPNs with our recommendations.
Two of the services are NordVPN and ExpressVPN.
Of course, the ideal solution would be for access point providers to enable encryption on your service, but this is not as simple as it sounds. As always, the biggest security threat lies in the need for convenience.

Most of these venues are informal spaces for customers, meaning they want to log in and log out quickly and seamlessly. Having to enter a password (or worse, a username and password) may not be that easy for some.
Although some hotels, restaurants, and other establishments already use encrypted Wi-Fi, in many cases the responsibility for protecting personal data rests firmly in your own hands.
One option is to simply avoid using any website or app where sensitive data is used while using the public Wi-Fi connection. But since this is inconvenient, the most feasible will be to use mobile data on your phone instead of Wi-Fi.
This is an encrypted connection, and you can generally set up a personal access point so that you can share that internet connection with a laptop, tablet, or any other worthwhile device.
Finally, it should be noted that some applications will use encryption even if the Wi-Fi connection is not encrypted. Banking apps are a good example, plus there are also messaging apps and email services that use their particular encryption.
How-To
How to Fix Blurred Images/Photos on Android Phones

Why your photos can be blurry (blurred) There are several factors that cause them, including: When taking photos it is unstable (shaky), the object you are photographing is a moving object, the camera lens is dirty, the camera application is not functioning properly and several other causes.
How to Fix Blurry Pictures Taken from Android Phone:
1. Use an app to fix blurry photos
Most image editing apps include a useful function to sharpen photos, this feature you can use to improve your Android photos.
As for the method, I have discussed it in a previous article here
Or you can also try other apps like VanceAI and Neural. love, Let’s Enhance, and MyEdit
2. Take precautions so that the photos are not blurry
Tips for preventing blurry images on Android phones, there are several things you can try to prevent this, including:
- Clean your phone lens
- Take photos in better lighting conditions
- Delete the Camera application cache, go to the menu: Settings > Storage > Devices > Cached data > Clear cached data > OK.
- As much as possible, avoid excessive zoom functions when taking photos on an Android cellphone camera.
How-To
How to Fix Spotify AI DJ Not Showing

As a music streaming service, Spotify has revolutionized the way we listen to music. One of its most exciting features is the AI DJ, which creates custom playlists based on your music preferences. However, sometimes users encounter an issue where the AI DJ feature is not showing up. In this article, we will go through a step-by-step guide on how to fix this issue.
Step 1: Check for Updates
The first thing you should do is check if your Spotify app is updated. If not, update it to the latest version. This may resolve any glitches or bugs that are causing the AI DJ feature to disappear.
Step 2: Clear Cache
Clearing the cache on your Spotify app may also help resolve this issue. To do this, go to your app settings and select “Storage.” From there, tap on “Clear Cache” and restart your app.
Step 3: Disable Battery Saver
Sometimes, battery saver settings can interfere with the app’s performance. To disable the battery saver, go to your phone’s settings and select “Battery.” From there, disable any battery-saving modes that are enabled.
Step 4: Check the Internet Connection
Make sure that you have a stable internet connection. If your internet connection is slow or unstable, the app may not be able to load the AI DJ feature.
Step 5: Check Country Settings
Spotify’s AI DJ feature is not available in all countries. If you’re using the app in a country where this feature is not available, it may not appear on your app. You can check the list of countries where the AI DJ feature is available on the Spotify website.
Step 6: Check the Subscription
The AI DJ feature is only available to Spotify Premium subscribers. If you’re using the free version of the app, you may not be able to access this feature.
Step 7: Reinstall the App
If none of the above steps work, you can try uninstalling and reinstalling the app. This will reset the app to its default settings, which may resolve any issues that were causing the AI DJ feature to disappear.
Step 8: Restart Your Device
If the issue persists, try restarting your device. This can help fix any software issues that may be causing the problem. Here’s how to do it:
- Press and hold the power button on your device.
- Tap on the “Restart” option when it appears on the screen.
- Wait for your device to restart, and then try opening the Spotify app again.
Step 9: Contact Spotify Support
If the issue persists after trying all the above steps, it’s time to contact Spotify support. You can reach out to them through their website, and they will guide you through resolving the issue.
Conclusion
Spotify’s AI DJ feature is a great way to discover new music based on your preferences. However, it can be frustrating if it’s not showing up on your app. By following the steps outlined above, you should be able to resolve the issue and get back to enjoying your music. Remember to check for updates, clear cache, disable battery saver, check internet connection, country settings, and subscription, and reinstall the app. If all else fails, don’t hesitate to contact Spotify support.
How-To
How to Overcome steam error code e84

The steam error code e84 problem usually occurs when we are about to log into the Steam platform, this error is also accompanied by Something that went wrong while attempting to sign you in.
If you are currently experiencing the same error. So in this article, we are going to provide you with the repair solution with the simplest way to fix it.
1. Delete Temporary Files
Temporary Files on your computer can sometimes make Steam run improperly. One is the steam error code e84, so try deleting temporary files from your computer. To do so, follow these steps:
- Press the Windows key + R then type the command %temp% and press the Enter / OK key
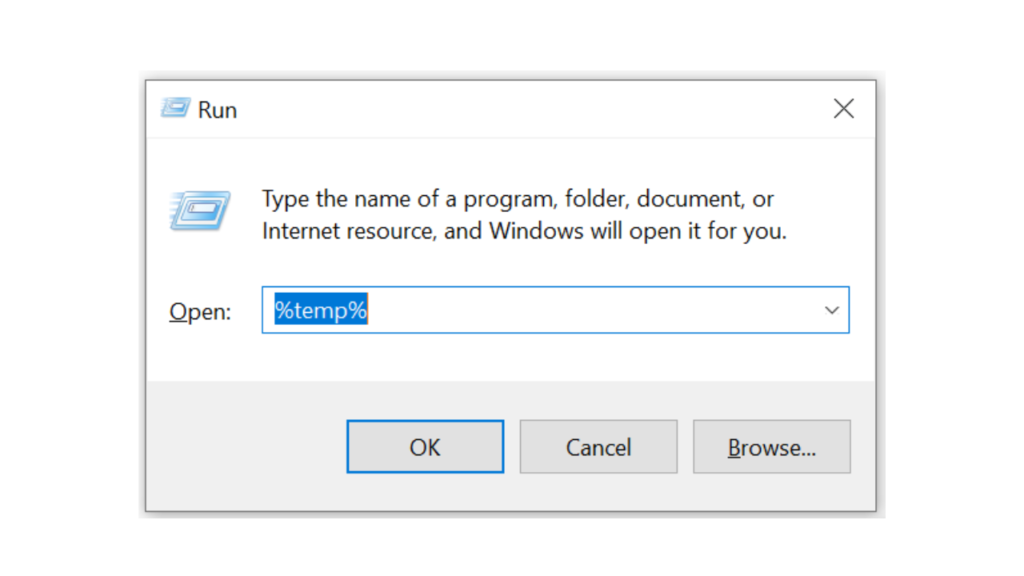
- Then delete all files and folders in the temp folder
- After that, try restarting your computer, and try opening Steam, is the error code E84 still there?
Deleting all of these folders will not cause errors or damage to the computer/programs on your computer, because all the files in this temp folder are temporary files that are no longer needed.
2. Update the Steam Application
Check if there is an update available for the steam application, if there is, please update immediately. And after the update is complete, try opening the Steam application again.
3. Reinstall the Steam App
If the two methods above don’t work, there could be some problematic or damaged Steam system files. The best solution is to reinstall the Steam application.
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone