Tech
Simjacker: You Can Spy On The Location Of Any Mobile With Simjacker
Simjacker:- Locate Any Mobile With Simjacker
Privacy has become one of the issues of most significant concern in the world of telecommunications. Mobile is a tool that always goes with us and, although it is beneficial, it can also be an open door for those who wish to violate our privacy.
Access to the location of a device is one of the most compromised. It is true that Android and iOS increasingly have better systems to protect our place, but what happens when this method can skip the systems directly attacking the SIM?
Simjacker Can Get The Location Of Any Mobile By Skipping Security
In recent hours, the security company AdaptativeMobile Security has published the existence of a mobile vulnerability that it has decided to call Simjacker.
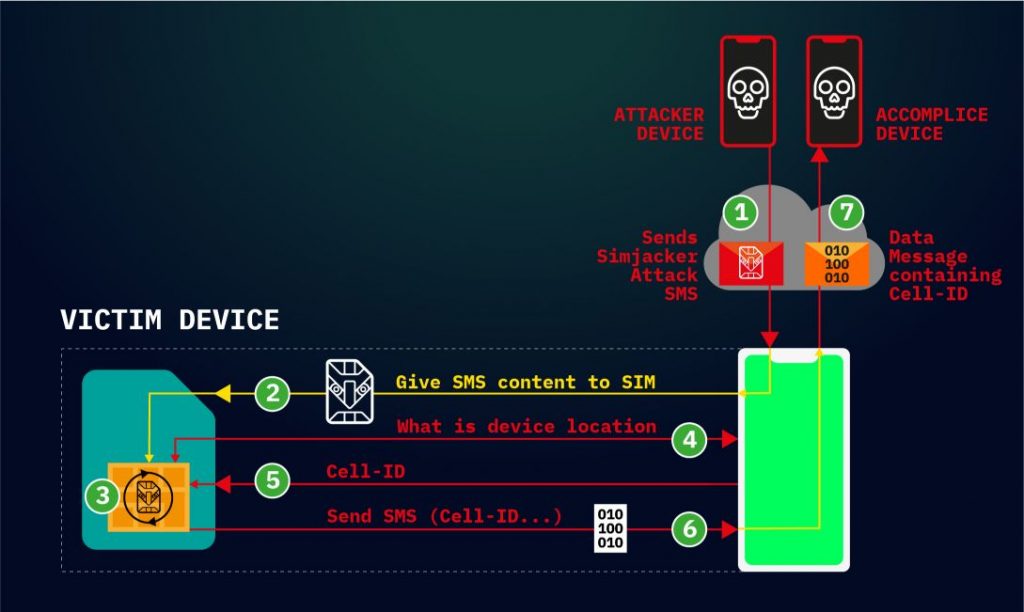
Image:- AdaptiveMobile
Roughly, Simjacker exploits the vulnerability of SIM cards to take control of some of our device data. The attack comes through an SMS that skips the operating system to access a piece of software known as S @ T Browser. Through this type of attacks on the SIM, it seems possible to spy on the location of any phone number.
One of the most significant risks to this attack is that, as users, we have no way of noticing this type of messages because, due to the format they use to attack us, those SMS never reaches the inbox of our mobile.
Beyond spying on the location: what is capable of achieving this type of attack?
The most striking case of Simjacker is to be able to spy on the location of our mobile by skipping the security criteria of our mobile operating system. But this would not end here because, with the appropriate UICC instructions, these types of attacks have the potential to take greater control of the smartphone. These would be some of the possibilities they wanted to highlight:
- Disinformation: send SMS and MMS with controlled content.
- Fraud: call premium numbers from our mobile.
- Espionage: beyond the location, making calls from the mobile itself to listen to the microphones.
- Malware deployment by opening specific web pages.
- Denial of service by canceling the SIM card.
- Device information (language, type of radio, battery level …).
Who Are These Attacks Affecting?
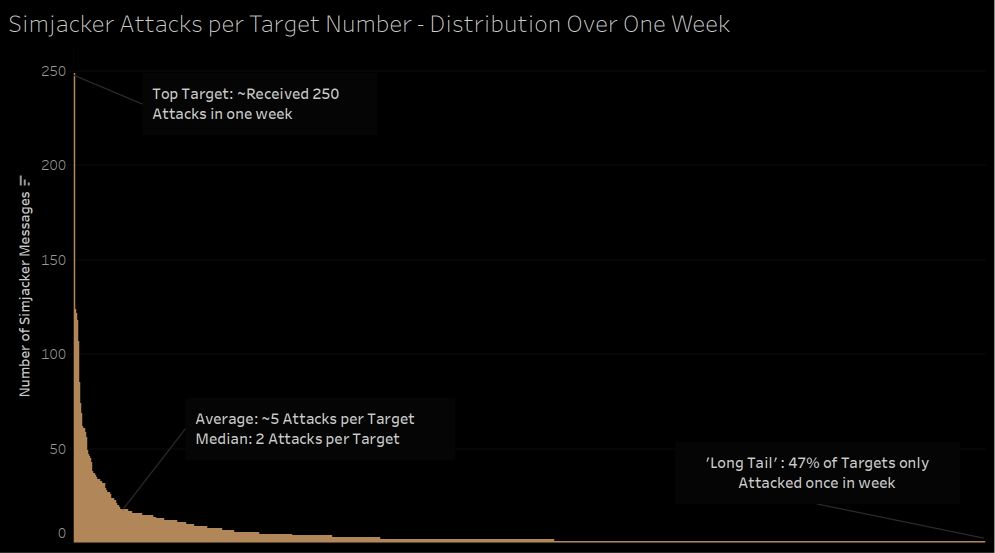
image:- AdaptiveMobile
According to the security agency, this security breach could have been used for the past two years. Without revealing specific information, they are quite confident that it would have been created by a private company that collaborates with governments.
In a specific country monitoring, they have been able to observe an average of 100-150 daily attacks. Based on these data, they have compiled a graph indicating the average number of attacks each telephone number receives; leaving some impressive figures:
- 47% of affected numbers received only one attack during the week.
- The average is two attacks per phone number.
- The average number of attacks received is five per number.
- There are a small number of numbers that receive dozens of attacks a week; There are even cases of 250 seizures a week.
What conclusions can we draw from these attacks? Far from becoming a mass surveillance cyber attack, Simjacker seems to be a surveillance tool for particular users. When the majority of mobiles receive a small number of attacks, it appears that they have been victims of the attack by a simple trial and error process; being discarded at the time of not being the objective.
Should We Worry?
AdaptativeMobile has commented that they will give more details about this vulnerability in the Virus Bulletin Conference in London, on October 3. Far from being a vulnerability to exploit, the objective of this discovery is to offer a solution.
On the part of the security company, they affirm that they have already begun to take the following measures:
- Working with operators: being an attack dependent on mobile networks, operators can identify these attacks and block them before they are useful.
- I am notifying the GSM association and the SIM Alliance.
In the end, in the face of such attacks, there is nothing we can do since we cannot take measures directly beyond asking our operators to work continually improving security.
If you want to know more about the technical details, we recommend you read the Adaptative Mobile Security article.
Tech
AI Alternative to GPT Chat
Recently, you may or have used ChatGPT. This chatbot is OpenAI (Artificial intelligence), which allows users to have conversations with AI. ChatGPT has emerged as a new innovation. With ChatGPT it has changed everything from creative writing to coding and even visual content creation.
In this article, we will provide information about popular ChatGPT alternatives that you can try. Whether it’s for text creation, research, coding, and visual creation.
The following are AI alternatives to GPT chat:
1. Google Bard
Google recently released a new feature called Google Bard, which is Google’s version of ChatGPT. Google Bard is an experimental conversational AI service. Bard is powered by Google’s latest PaLM 2 LLM.
You can use Google Bard as a generative AI for searches, creating presentations, creating speech scripts, and several other features. You’ll immediately see quick answers to questions at the top of the search results. Not to mention, you can also upload images to Google Bard.
Google Bard is quite curious, so we tried to make a comparison between ChatGPT vs Google Bard.
So we can conclude that Google Bard has the following features: Image upload, Chat history, Supported by the latest PaLM 2 model, Export to Document, Colab, Coding capabilities, Multilingual model, Implicit Code Execution
2. Microsoft Bing AI
Microsoft Bing AI. The updated search engine is powered by an optimized ChatGPT model, which Microsoft initially referred to as the Prometheus model, after which it was later confirmed as GPT-4.
Bing-ChatGPT is the new Bing also has a Chat mode that pulls in web queries and allows us to ask for contextual information based on those queries. This Bing bot AI search engine recently received a number of new features, including multimodal capabilities, visual answers, improved accuracy, and Bing Image Creator.
Bing even lets users plan trips, get recipes, seek advice, and more, just like ChatGPT.
Key Features of this Bing AI are supported by GPT-4, Supports visual input and output, Connect to the internet, Getting the latest information on any subject, Chat history, and Different chat modes.
3. Perplexity AI
Perplexity AI is another ChatGPT alternative that you can try. What differentiates this from other AIs is that Perplexity AI has an OpenAI API and, thus, performs well with good responsiveness.
If you visit the Perplexity AI website, it has been packaged in a minimalist and easy-to-use way. So it is easy and simple to use. The tool offers ChatGPT-like functionality, including the ability to host conversations and provide a variety of simple responses. However, unlike ChatGPT, Perplexity even cites the sources it uses to answer your questions.
Tech
Can AI Technology Replace Human Jobs? This is ChatGPT Answer!

Much has been said about AI chatbots such as ChatGPT, Bing AI, and Google Bard, about whether in the future these tools can replace human work or not.
Recently, ChatGPT by OpenAI answered this question in great detail. What’s the answer?
ChatGPT says that AI-based chatbots can automate several jobs such as customer service, data entry, basic information retrieval, and many others.
This could certainly lead to some job shifts, but would not replace human workers directly.
“As an AI language model, I don’t have the ability to automate jobs or replace human workers directly. However, AI-powered chatbots like ChatGPT can affect certain jobs indirectly,” said ChatGPT, quoted from India Today.
“AI chatbots, including ChatGPT, have the potential to automate certain tasks previously performed by humans, potentially resulting in job shifts across several industries. Routine and repetitive tasks, such as customer service, data entry, and basic information retrieval, are more vulnerable to automation through chatbots,” he continued.
However, ChatGPT explains that it can also create new jobs that will benefit humans.
“The development, implementation, and maintenance of AI chatbots require specific skills such as AI programming, natural language processing, and data analysis, which can create new job opportunities in this field,” he explains.
Furthermore, ChatGPT emphasized that it is difficult for AI to replace human work as a whole because AI cannot imitate the natural sense of empathy, critical thinking, and problem-solving that every human has.
On the other hand, Bing AI said that this chatbot was designed to help humans and not harm them.
“Humans have nothing to fear from AI chatbots like ChatGPT because they are designed to help humans, not hurt them. AI chatbots are neither intelligent nor evil. They are only capable of doing what humans are programmed to do. They have no intentions or emotions of their own. They are tools that can assist humans with various tasks such as answering questions, booking meetings, composing emails, and more,” said Bing AI.
Tech
Samsung Releases AC WindFree Ultra, Saves Electricity and Can Filter Pollution

Samsung officially introduced its newest AC product in the WindFree Ultra series today, Monday (3/4).
Samsung WindFree Ultra is a smart air conditioner with air purification capabilities that are expected to be able to bring healthy air into the room.
AC SamsungWindFree Ultra is supported by Air Purification PM 1.0 Filter technology which is capable of capturing very fine particles.
Samsung claims that this smart AC is also able to sterilize more than 99% of bacteria.
The Samsung WindFree Ultra filter can be washed and used continuously so users don’t have to pay more for indoor air purification.
This device is also equipped with an indicator light, helping users to know the air quality in the room quickly.
Support Auto Cooling and Fast Cooling
Samsung WindFree Ultra comes with a fast cooling technology called WindFree Cooling.
When the new AC is turned on, the Fast Cooling feature will cool the room quickly. Furthermore, when the desired temperature has been reached, the WindFree Cooling feature is activated to maintain that temperature and provide an ideal comfort level.
When WindFree Cooling is active, cool air is distributed through 23,000 micro-holes in the body of the AC unit, allowing users to move, relax, and rest comfortably without being directly hit by cold winds.
When WindFree Cooling is working, this smart AC will also consume minimal electrical power, up to 77% more efficiently than the Fast Cooling feature.
This technology is also equipped with a Motion Detect Sensor which automatically changes the mode to save electricity when no one is in the room.
Saving electricity
Samsung AC WindFree Ultra already uses the Digital Inverter Boost energy-saving compressor.
This compressor allows the consumer to maintain the desired temperature while reducing energy consumption.
The Digital Inverter Boost compressor dramatically reduces the time it takes for the compressor to reach maximum power after start-up, cooling air 43% faster and reducing energy use by up to 73% compared to conventional air conditioners.
The lowest power consumption point obtained by this device can reach 180 Watts so the Samsung AC WindFree Ultra has received the highest rating, namely 5 stars for CSPF (Cooling Seasonal Performance Factor) Certification.
For more information and information regarding Samsung WinFree Ultra AC products, you can visit Samsung’s official website .
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone