How-To
How to encrypt or protect my emails easily and quickly

The security of emails is very important when they are sent to other people. Its encryption or protection is very common, having ways to do it easily and quickly.
This helps to avoid actions by hackers on the accounts, making it a widely used alternative. Normally, most Gmail emails have protection made by its users to secure their information.
There are ways to encrypt the different types of emails out there. To know the most convenient, here you can find the one corresponding to your email.
Ways to encrypt or protect emails
Gmail
The best-known way to encrypt Gmail email is by providing a password for it. The recipient will be the only one who can have this password, making it possible for the email to be decrypted.
The entire process is carried out with an encryption algorithm with the key, transforming a readable language so that it is encrypted. With an extension for Google Chrome, encryption can be done for free, which is called “ Secure Mail for Gmail ”.

Once the extension is installed, go to the Gmail address, entering the email and there you will see the change. This will be a button to the right of the “Compose” option, it is a padlock used to encrypt.
When the padlock is pressed, the common components of an email will be entered, but with the red top bar. Thus, the mail is encrypted and after writing it, press ” Send Encrypted “, having to enter an encryption password.
The recipient of the email will need it to unblock the content of the message, having to also have the extension for Google Chrome. You will notice that when you open the mail, there will be a yellow text box that says: “ This message is encrypted. Decrypt message with password ”.
By clicking on that place in the email, a box will open to place the established password. Thus, you can easily encrypt or protect your mail and its content quickly.
Outlook
Before sending secret admin messages with Outlook, you need a digital certificate. You must enter “File”, “Options”, “Trust Center”, “Trust Center Settings”, “Email Security” and ” Obtain a Digital ID “.
The options are in that order, then choosing the certification for which the Digital ID is wanted. At that moment an email will arrive, obtaining the certificate to begin the encryption process.
Select “Tools”, then “Options” and click on “Security”, writing the name you want in ” Name of security settings “. Be sure that S / MIME was selected in the “Encryption Format” listing.
Under “Certificate of algorithms”, you will find “Certificate of the signature” and that option will be given in “Choose”. In “Select certificate”, you go to choose “Secure email certificate”, if you have not already chosen one.
Then, check the box ” Send these certificates with signed messages “, then click “OK” to save the changes. Based on this, in each of the emails, the Outlook digital signature will be placed.
Each signature must be sent to the recipients of the emails so that they can decrypt the content of the message.
How to encrypt other emails?
The emails in iOS, OSX, or Android can be encrypted if such devices allow them. In the case of using a Gmail account on Android, each email sent from there can be encrypted.

This is possible if the device has the encryption extension that is necessary to do this task. In the case of iOS devices, it is known that the system is a little more exclusive and its encryption operation is different.
In order to determine how to do this, you must go to the email security settings. There, following the encryption steps, security can be improved quickly and easily.
Fortunately, the best email providers make this security task possible at all times. Thus, writing an email becomes safe and the content of each message can be as confidential as you prefer.
How-To
How to Fix Blurred Images/Photos on Android Phones

Why your photos can be blurry (blurred) There are several factors that cause them, including: When taking photos it is unstable (shaky), the object you are photographing is a moving object, the camera lens is dirty, the camera application is not functioning properly and several other causes.
How to Fix Blurry Pictures Taken from Android Phone:
1. Use an app to fix blurry photos
Most image editing apps include a useful function to sharpen photos, this feature you can use to improve your Android photos.
As for the method, I have discussed it in a previous article here
Or you can also try other apps like VanceAI and Neural. love, Let’s Enhance, and MyEdit
2. Take precautions so that the photos are not blurry
Tips for preventing blurry images on Android phones, there are several things you can try to prevent this, including:
- Clean your phone lens
- Take photos in better lighting conditions
- Delete the Camera application cache, go to the menu: Settings > Storage > Devices > Cached data > Clear cached data > OK.
- As much as possible, avoid excessive zoom functions when taking photos on an Android cellphone camera.
How-To
How to Fix Spotify AI DJ Not Showing

As a music streaming service, Spotify has revolutionized the way we listen to music. One of its most exciting features is the AI DJ, which creates custom playlists based on your music preferences. However, sometimes users encounter an issue where the AI DJ feature is not showing up. In this article, we will go through a step-by-step guide on how to fix this issue.
Step 1: Check for Updates
The first thing you should do is check if your Spotify app is updated. If not, update it to the latest version. This may resolve any glitches or bugs that are causing the AI DJ feature to disappear.
Step 2: Clear Cache
Clearing the cache on your Spotify app may also help resolve this issue. To do this, go to your app settings and select “Storage.” From there, tap on “Clear Cache” and restart your app.
Step 3: Disable Battery Saver
Sometimes, battery saver settings can interfere with the app’s performance. To disable the battery saver, go to your phone’s settings and select “Battery.” From there, disable any battery-saving modes that are enabled.
Step 4: Check the Internet Connection
Make sure that you have a stable internet connection. If your internet connection is slow or unstable, the app may not be able to load the AI DJ feature.
Step 5: Check Country Settings
Spotify’s AI DJ feature is not available in all countries. If you’re using the app in a country where this feature is not available, it may not appear on your app. You can check the list of countries where the AI DJ feature is available on the Spotify website.
Step 6: Check the Subscription
The AI DJ feature is only available to Spotify Premium subscribers. If you’re using the free version of the app, you may not be able to access this feature.
Step 7: Reinstall the App
If none of the above steps work, you can try uninstalling and reinstalling the app. This will reset the app to its default settings, which may resolve any issues that were causing the AI DJ feature to disappear.
Step 8: Restart Your Device
If the issue persists, try restarting your device. This can help fix any software issues that may be causing the problem. Here’s how to do it:
- Press and hold the power button on your device.
- Tap on the “Restart” option when it appears on the screen.
- Wait for your device to restart, and then try opening the Spotify app again.
Step 9: Contact Spotify Support
If the issue persists after trying all the above steps, it’s time to contact Spotify support. You can reach out to them through their website, and they will guide you through resolving the issue.
Conclusion
Spotify’s AI DJ feature is a great way to discover new music based on your preferences. However, it can be frustrating if it’s not showing up on your app. By following the steps outlined above, you should be able to resolve the issue and get back to enjoying your music. Remember to check for updates, clear cache, disable battery saver, check internet connection, country settings, and subscription, and reinstall the app. If all else fails, don’t hesitate to contact Spotify support.
How-To
How to Overcome steam error code e84

The steam error code e84 problem usually occurs when we are about to log into the Steam platform, this error is also accompanied by Something that went wrong while attempting to sign you in.
If you are currently experiencing the same error. So in this article, we are going to provide you with the repair solution with the simplest way to fix it.
1. Delete Temporary Files
Temporary Files on your computer can sometimes make Steam run improperly. One is the steam error code e84, so try deleting temporary files from your computer. To do so, follow these steps:
- Press the Windows key + R then type the command %temp% and press the Enter / OK key
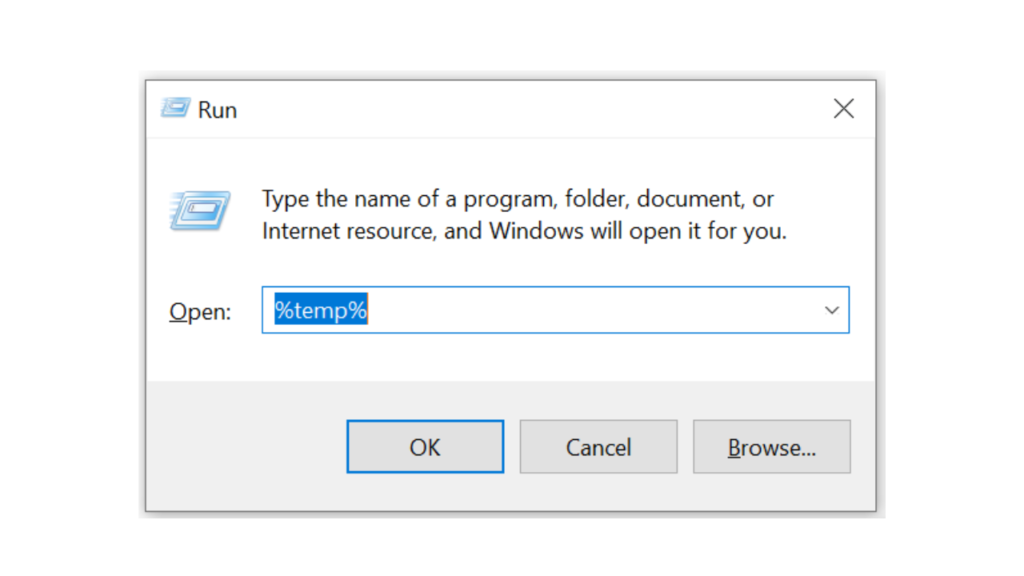
- Then delete all files and folders in the temp folder
- After that, try restarting your computer, and try opening Steam, is the error code E84 still there?
Deleting all of these folders will not cause errors or damage to the computer/programs on your computer, because all the files in this temp folder are temporary files that are no longer needed.
2. Update the Steam Application
Check if there is an update available for the steam application, if there is, please update immediately. And after the update is complete, try opening the Steam application again.
3. Reinstall the Steam App
If the two methods above don’t work, there could be some problematic or damaged Steam system files. The best solution is to reinstall the Steam application.
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone