How-To
Best Free VPNs of 2021

There are several virtual private networks on the market, commonly known as VPN (a virtual private network), which can be downloaded from their website completely free of charge.
In general, all of them will allow you to use the Internet anonymously and change the location of your IP so that you can access that content blocked in your country and available only in another or others.
But before you drown in the sea of options that you have at your disposal, at PCWorld Spain we have done the fieldwork for you, and today we bring you the best free VPNs today.
Is there a completely free VPN?
Yes, of course, and in this article, you will not only find one, but we list several VPN services that are completely free. We understand that you ask yourself this question since you have to be very careful.
Unlike free antivirus, which is almost as good as its paid versions, free VPNs are quite restrictive in terms of the data limit you can use, the number of servers, and even your browsing speed.
Is it safe to use a free VPN?
Yes, it can be. There is practically no difference in the technology used in a paid VPN and a free VPN, which means that you have access to the same security and the same privacy in both cases.
Now, on rare occasions, when you use a free VPN you also give the company permission to use your data and sell it to third parties. This is not the case for the services listed in this article, but if you opt for another, be sure to read the terms of use well.
Are free VPNs worth it?
It may be good for you to use a VPN with a data or server limit, especially if the only thing you are going to use it for is to protect the security of your device when using public Wi-Fi. Now that will mean that you probably can’t watch videos online.
Once you have reached the data limit, you will have no choice but to uninstall that VPN and look for another one that is also free, wait for the data to be reset the following month, or simply pay to use its unlimited service.
Now there are exceptions. ProtonVPN offers unlimited data for free and Hide.me has just changed its offer so that once the data limit is exceeded, you can continue using their service but without the possibility of choosing the server you want.
After hours of trying VPN, both free and paid, it is quite evident to us that you will end up seeing many advantages when you spend a few euros a month for a service like NordVPN, PureVPN, Surfshark, or CyberGhost.
But as we said, if you have never used a VPN, it is better that you start by trying one of the options that we give you below. ProtonVPN is our first recommendation, although there is server restriction and it can only be used on one device.
There are other ways to hide your IP address, but using a VPN is still the best option for most.
Best Free VPNs of 2021
ProtonVPN
From free ($ 5 per month for Basic)
The ProtonVPN is the only software of its kind that we know that offers a completely free full service. In this sense, it is not funded by ads and still does not impose speed restrictions or data limits.
The operation of this VPN is very simple and secure, especially since it works under the zero-logs policy, which means that no information is stored on the server and that ensures your anonymity. In addition, it follows the Swiss data protection policy.
Obviously, not everything is perfect and there are certain restrictions. Surely the one that can affect you the most is that you only have the possibility of connecting to servers in three different countries: the United States, the Netherlands, and Japan.
That means, for example, that if you are outside of Spain and want to see content that can only be seen in Spanish territory, ProtonVPN will be of no use to you. Instead, it is very useful for watching Hulu or Disney + content limited to the United States.
On the other hand, another major drawback is that you can only use your account on a single device. However, it is the least restrictive free VPN that we know of and that is why it is the one we recommend the most.
Windscribe
Free
Although not as good as its paid version, the free Windscribe VPN connection also offers very useful features that will help you keep your identity private and trick your browser into thinking that you are in a different city.
Among the benefits that you will get when you download Windscribe, we highlight the possibility of using it on an unlimited number of devices, so that you can use the same account on all your computers and laptops.
In addition, you can protect your device from viruses and malware content with the built-in firewall, and say goodbye to annoying and tiresome ads with an excellent adblocker.
Of course, among its limitations is the fact that you can only choose between 11 servers, which means that you can only change your IP for another from 11 different locations. In the paid version, you can choose between 50 countries.
On the other hand, if you download Windscribe to your device for free, you can only use a maximum of 10 gigs per month. That means that once used, your computer or laptop will no longer be protected.
Hide.me

Free
Hide.me‘s VPN has a data transfer limit, in this case, 2GB. Whoever wants to have more, can opt for the Plus share -with 75 GB at your disposal- or, better still, with the Premium share with unlimited data.
This means that customers who choose to use the network for free will surely not be able to enjoy high-quality videos, although the broadband it offers may be sufficient to surf the Internet.
The free registration also allows you to simultaneously connect only one device, be it Windows, macOS, Android, iOS, or Linux. On the other hand, with the Premium account, you can enjoy your private connection on five devices at the same time.
It is true that the subscription has more advantages than betting on free, but it is no less true that the free option is one of the best of all that we have tried. It will also help you to know if it is worth paying for it or not.
With any of its paid subscriptions, yes, you will enjoy maximum privacy and freedom of expression, since it will also unblock the most popular restricted sites of the country in which you are.
TunnelBear
From $ 4.19 per month
The first drawback of the TunnelBear VPN used to be that it did not operate from Spain, so users residing in Spain could only use it to consult pages only available in their country when they are abroad.
Now it is no longer the case. In addition, this service has servers also operating from the United States, United Kingdom, Canada, Germany, France, and Japan. It can also be used from Australia but only if a paid subscription plan is contracted.
One of the most attractive features of this VPN is undoubtedly the high speed it can reach: about 12 MB per second, and also both the installation process and the use of the interface are very intuitive.
TunnelBear seems very suitable for protecting your browsing data when connecting to a public Wi-Fi network, especially thanks to the ‘Vigilant Mode’ function, which blocks any suspicious content when you lose connection to the private network.
If you hesitate between betting on the free service or choosing one of the two premium installments, keep in mind that the zero-cost option has a limit of 500 MB per month, which you can increase up to one GB if you write a tweet talking about TunnelBear.
Hotspot Shield
From $ 3.49 per month
Hotspot Shield‘s virtual private network is one of the most used by Internet users, probably because it does not set any data transfer limits and also offers a more than sufficient download speed: 6.5 MB per second.
However, it has certain disadvantages compared to the paid versions. First of all, the free VPN is financed exclusively by advertisers, which means that by installing it you will accept the presence of annoying ads while browsing the net.
In addition, indirectly you will also be giving it permission to change certain configurations of your operating system, such as the web browser that you have by default.
On the other hand, subscribing for free to this VPN is only recommended if you want to access exclusive content for residents of the United States since the service will assign you a random server based in this country.
And even so, the free option will block certain pages of popular use in the North American country. Despite all this, it is a VPN to consider if you are only looking for safe Internet browsing and that is protected from possible computer attacks by hackers.
How-To
How to Fix Blurred Images/Photos on Android Phones

Why your photos can be blurry (blurred) There are several factors that cause them, including: When taking photos it is unstable (shaky), the object you are photographing is a moving object, the camera lens is dirty, the camera application is not functioning properly and several other causes.
How to Fix Blurry Pictures Taken from Android Phone:
1. Use an app to fix blurry photos
Most image editing apps include a useful function to sharpen photos, this feature you can use to improve your Android photos.
As for the method, I have discussed it in a previous article here
Or you can also try other apps like VanceAI and Neural. love, Let’s Enhance, and MyEdit
2. Take precautions so that the photos are not blurry
Tips for preventing blurry images on Android phones, there are several things you can try to prevent this, including:
- Clean your phone lens
- Take photos in better lighting conditions
- Delete the Camera application cache, go to the menu: Settings > Storage > Devices > Cached data > Clear cached data > OK.
- As much as possible, avoid excessive zoom functions when taking photos on an Android cellphone camera.
How-To
How to Fix Spotify AI DJ Not Showing

As a music streaming service, Spotify has revolutionized the way we listen to music. One of its most exciting features is the AI DJ, which creates custom playlists based on your music preferences. However, sometimes users encounter an issue where the AI DJ feature is not showing up. In this article, we will go through a step-by-step guide on how to fix this issue.
Step 1: Check for Updates
The first thing you should do is check if your Spotify app is updated. If not, update it to the latest version. This may resolve any glitches or bugs that are causing the AI DJ feature to disappear.
Step 2: Clear Cache
Clearing the cache on your Spotify app may also help resolve this issue. To do this, go to your app settings and select “Storage.” From there, tap on “Clear Cache” and restart your app.
Step 3: Disable Battery Saver
Sometimes, battery saver settings can interfere with the app’s performance. To disable the battery saver, go to your phone’s settings and select “Battery.” From there, disable any battery-saving modes that are enabled.
Step 4: Check the Internet Connection
Make sure that you have a stable internet connection. If your internet connection is slow or unstable, the app may not be able to load the AI DJ feature.
Step 5: Check Country Settings
Spotify’s AI DJ feature is not available in all countries. If you’re using the app in a country where this feature is not available, it may not appear on your app. You can check the list of countries where the AI DJ feature is available on the Spotify website.
Step 6: Check the Subscription
The AI DJ feature is only available to Spotify Premium subscribers. If you’re using the free version of the app, you may not be able to access this feature.
Step 7: Reinstall the App
If none of the above steps work, you can try uninstalling and reinstalling the app. This will reset the app to its default settings, which may resolve any issues that were causing the AI DJ feature to disappear.
Step 8: Restart Your Device
If the issue persists, try restarting your device. This can help fix any software issues that may be causing the problem. Here’s how to do it:
- Press and hold the power button on your device.
- Tap on the “Restart” option when it appears on the screen.
- Wait for your device to restart, and then try opening the Spotify app again.
Step 9: Contact Spotify Support
If the issue persists after trying all the above steps, it’s time to contact Spotify support. You can reach out to them through their website, and they will guide you through resolving the issue.
Conclusion
Spotify’s AI DJ feature is a great way to discover new music based on your preferences. However, it can be frustrating if it’s not showing up on your app. By following the steps outlined above, you should be able to resolve the issue and get back to enjoying your music. Remember to check for updates, clear cache, disable battery saver, check internet connection, country settings, and subscription, and reinstall the app. If all else fails, don’t hesitate to contact Spotify support.
How-To
How to Overcome steam error code e84

The steam error code e84 problem usually occurs when we are about to log into the Steam platform, this error is also accompanied by Something that went wrong while attempting to sign you in.
If you are currently experiencing the same error. So in this article, we are going to provide you with the repair solution with the simplest way to fix it.
1. Delete Temporary Files
Temporary Files on your computer can sometimes make Steam run improperly. One is the steam error code e84, so try deleting temporary files from your computer. To do so, follow these steps:
- Press the Windows key + R then type the command %temp% and press the Enter / OK key
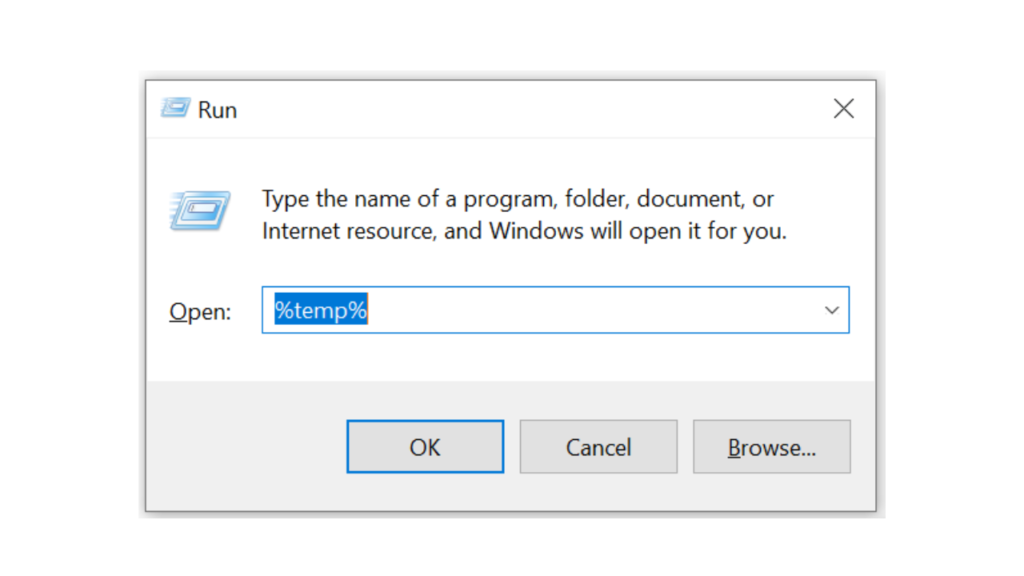
- Then delete all files and folders in the temp folder
- After that, try restarting your computer, and try opening Steam, is the error code E84 still there?
Deleting all of these folders will not cause errors or damage to the computer/programs on your computer, because all the files in this temp folder are temporary files that are no longer needed.
2. Update the Steam Application
Check if there is an update available for the steam application, if there is, please update immediately. And after the update is complete, try opening the Steam application again.
3. Reinstall the Steam App
If the two methods above don’t work, there could be some problematic or damaged Steam system files. The best solution is to reinstall the Steam application.
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone