Linux
Linux Kernel 5.16 Brings Significant Improvements to AMD CPUs
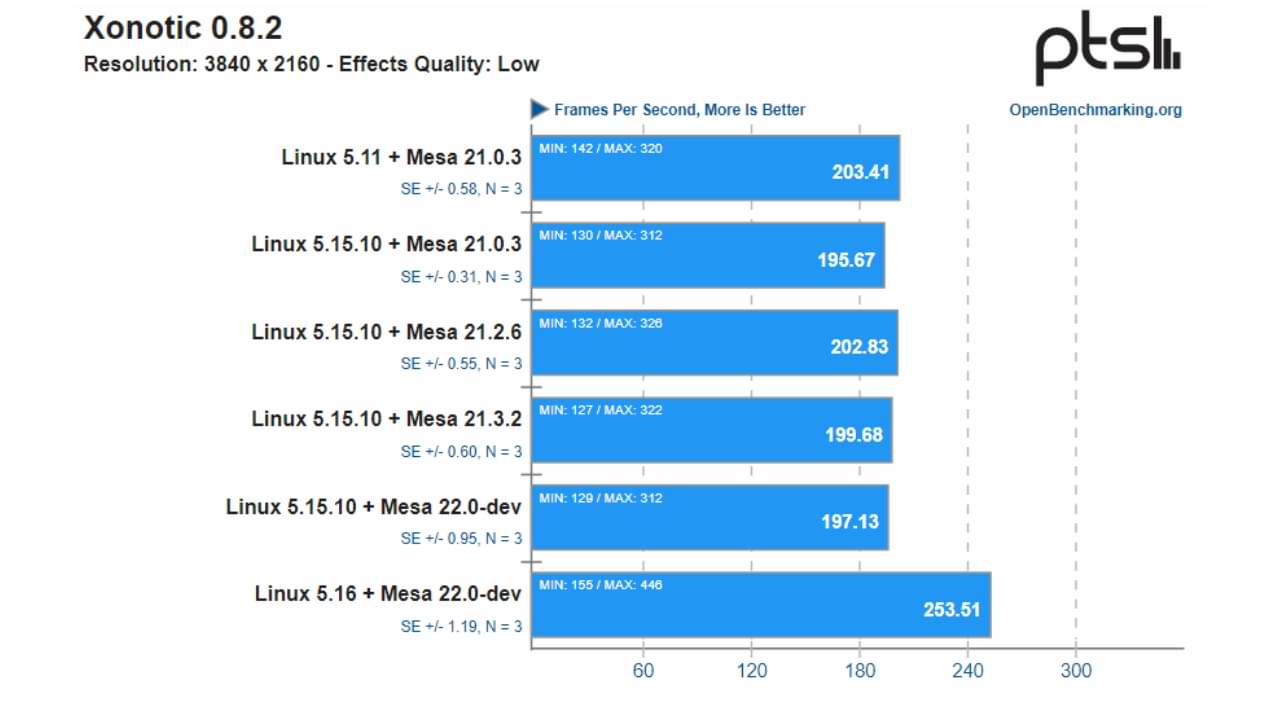
If you are a Linux user, especially if you are also an AMD user, then you must know that in Kernel 5.16 later, there will be a significant increase in AMD Ryzen CPU performance.
Based on the outstanding benchmarks, there is an increase of 28% from the Kernel 5.15 version that was present before, you can see the following benchmark results:
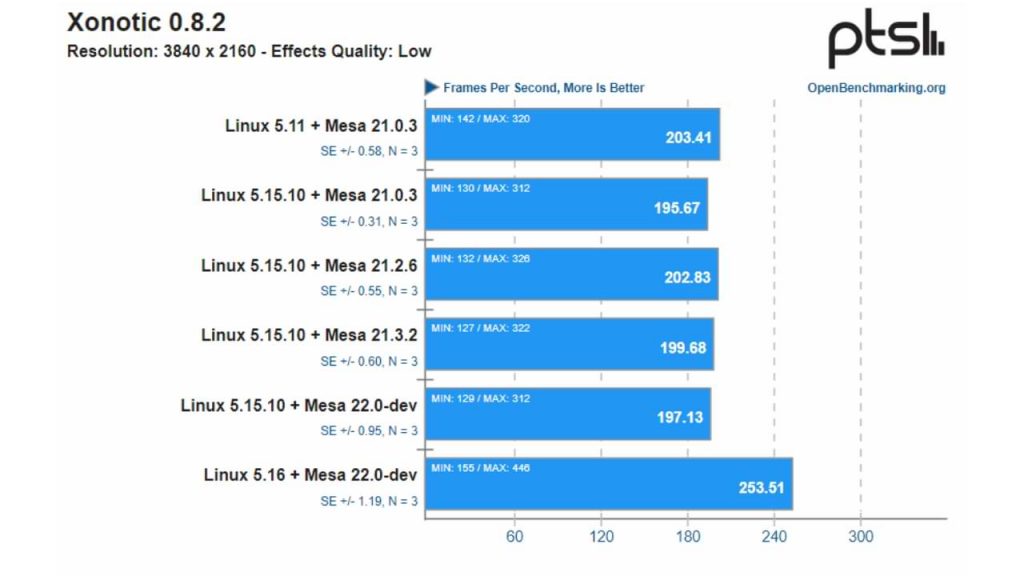
The benchmark above was carried out on a Lenovo ThinkPad T14s Gen2 laptop with Ryzen 7 PRO 5850U. the CPU 5850U is an octa-core processor based on the Zen 3 with 16 threads belonging to the AMD Cezanne APU lineup.
To see if the performance improvements also hold upon other Zen architectures, the Ryzen 5 5500U also did not escape the testing process, where there appeared to be a significant performance increase.
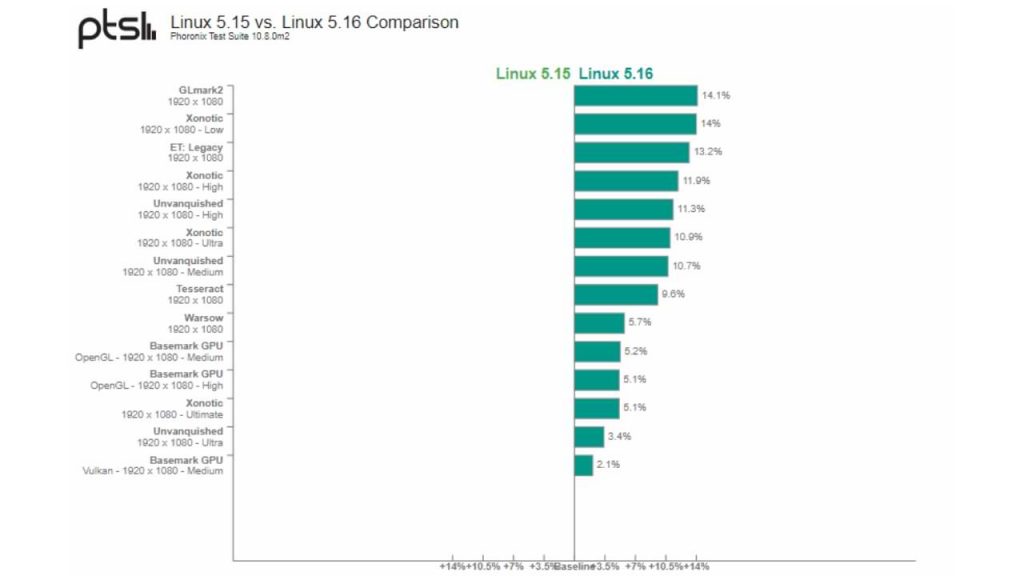
Reporting from Phoronix, Phoronix speculates that the noted performance gains may be due to a combination of CPU-specific optimizations:
“This improvement with Linux 5.16 was fascinating and came unexpectedly. Linux 5.16 has many new features including AMDGPU kernel driver improvements, but this Radeon Vega graphics boost came as a surprise as there wasn’t any announced optimization and the Vega graphics support at this stage is quite mature. It may also be a combination of CPU-related improvements with Linux 5.16.” Tulis Phoronix
Well, of course, this increase will be interesting for you Ryzen CPU users, but it’s not clear whether the upgrade will be present in all Ryzen series? or any other AMD series.
What do you think? comment below guys.
Via : Phoronix
Linux
2 Easy Ways to Format Flashdisk on Ubuntu Linux, which method do you choose?

Flash format is an activity that aims to empty the files stored in it. This method is done for various reasons, such as wanting to copy new files, removing viruses, and others.
Flash format in Linux is not much different from the flash format in Windows, and it’s just that there are various ways of formatting that you can do. Depending on your understanding of which one is easy, you can use your method.
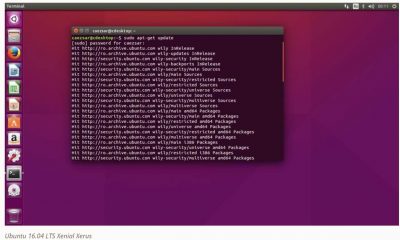
In this discussion, I will use two of the most common and easy-to-use ways to format a flash drive on Linux, namely how to format a flash drive manually and via the Terminal. The Type of Linux that I use here is the desktop version of Ubuntu 16.04.
How to Format Flashdisk on Linux Ubuntu
( I. ) Format Flash Disk Manually
The one most often used by users is how to format the flash here manually I use. The steps are as follows.
1. Open your file explorer or directory. Click on the flash drive that you want to format to see if your flash drive is legible, what it contains, and are you sure you want to format it.
2. After that, right-click on your flash device, as shown in the picture—Click Format to empty your flash.
3. Next, there are options ( Erase, Type, and Format ) that you can adjust to your needs on this Volume Format. You can follow the default options as shown in the picture.
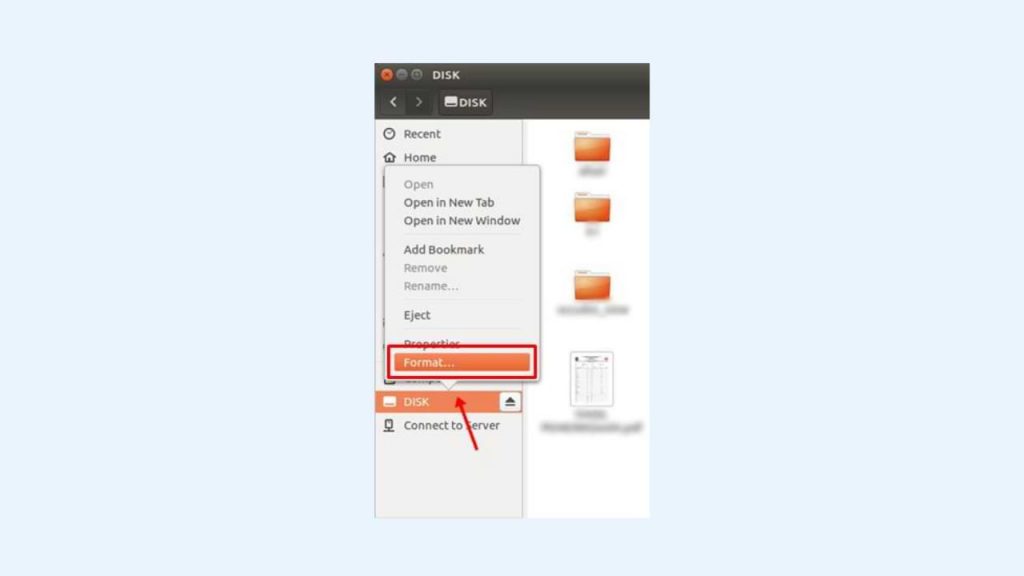
- I select ‘ Don’t overwrite existing data (Quick )’ in the Erase section. This option makes the formatting process faster.
- I choose the FAT format for Type here, but you can select another such as NTFS.
- Then, write a new name for your flash device in the Name field.
- Next, click the Format button.
4. After that, a confirmation will appear again to make sure you do the correct format of the flash. At this stage, the Type of your flash device will be displayed as indicated by the arrow in the image. The flash that I formatted is branded HP and has a capacity of 16GB. Click the Format button to start the flash format process.
5. Format your flash drive has been successful. You can check it by re-opening your flash directory and seeing that the flash drive is empty.
( II. ) Format the flash drive via Terminal.
In addition to manually, you can format the flash via the Terminal. How to? Follow these steps.
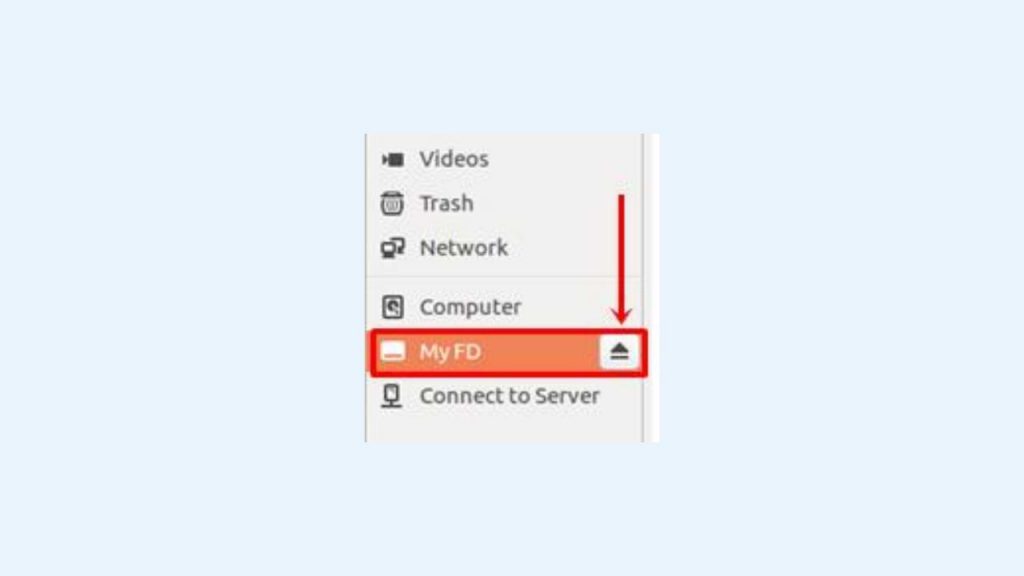
1. First, you can check the contents of your flash drive first to make sure you format it. Here, the name of my flash is My FD.
2. Open your Terminal. You can use the shortcut by pressing the keyboard’s Ctrl + Alt + T keys. Type the command:
sudo fdisk -lThe above command aims to find out the address of your flash drive. In the command, use the word sudo, where the Terminal will ask for your password input first. Enter your password; then, the Terminal will display the specifications of the device installed on your computer.
The device that is connected is the flash that we will format. You can ensure the device is your flash drive by observing its size. The example image above says 15.1 G, which means that the flash that I will format is filled with 15.1 GB. Then, remember the address. The address is listed in the Device column, wherein the image above it says /dev/sdb1.
3. Next, use the flash address we know earlier to run the umount command. This command aims to release the flash that is currently associated. You can see the related flash disk in the file explorer, wherein the flash name has an arrow button, as shown below.
Use the command below to remove your pen drive.
sudo umount /dev/sdb14. Next, you can type a command like the one below to format the flash drive.
sudo mkfs.vfat /dev/sdb1There is the word ‘ vfat ‘ in the command where FAT states the flash format after formatting. You can replace it with NTFS, hfs, ext2, ext3, ext4, and others according to your needs.
5. Finally, your flash is successfully formatted. To check, please open your file explorer and prove your flash drive is empty.
Before formatting the flash drive, make sure there are no important files that will be deleted. Back up your precious data if you are worried about losing your files. That’s how to format the flash on Linux Ubuntu easily. Give your feedback in the comments column below. Thank you.
Linux
How to Install Microsoft Teams on Linux
For those who don’t know, Microsoft Teams is now available as a Multi-Platform application on almost all operating systems, be it Windows, Mac, Linux, Android or iOS.
Now about this, we will summarize the short steps on how to Install Microsoft Teams on Linux. As usual, here, I will use Elementary OS as my mainstay Linux OS.
Here are the short steps.
Step 1. First, please open the Microsoft Teams site.
Step 2. Please download the Installer file from Microsoft Teams; please adjust it to the Linux distro you have, DEB for Ubuntu, Debian and all their descendants, and RPM for Fedora, CentOS and all their siblings.
Step 3. After the file is downloaded, please open the file, and if your Linux already has an app installer, the steps will be easier because we click install.
But if it doesn’t exist, we can use the classic steps by using Terminal. Open Terminal > Go to Directory Download > Then type the following command:
sudo dpkg -i <namafileinstaller>Exactly as in the picture above, after typing the command, you need to enter your root password, and then the installation will run until the Microsoft Teams application is installed.
Well, please try, guys; it’s easy, isn’t it? I hope this article is useful.
Linux
GParted, Partition Management Application for Linux Operating System
Have you ever heard of GParted? This name may still sound less familiar to your ears, especially for those who use the Windows operating system because GParted is intended for Linux users.
Although it sounds less familiar, this application is quite a lot of people who use it. One of the reasons is because GParted offers ease of operation. Even people new to using it tend not to experience complicated problems even though it is the first time they try it.
What Are the Features of GParted?
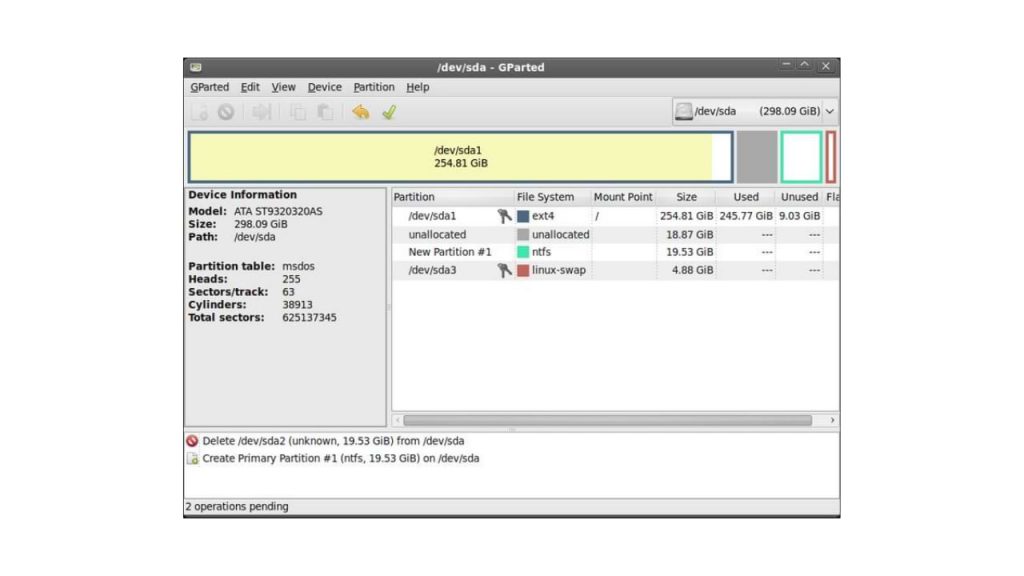
GParted is an application that can run on both x86 and x64 computers with operating systems such as Windows, Mac OS, and Linux with a minimum RAM size of 256 MB. From these specifications, we can know that this application is light because it only requires a RAM capacity of only 256 MB.
Some of the features that make GParted one we recommend include:
- Create or delete partitions
- Format partition
- Resize partition
- Mounting and unmounting partitions _
- Label
- Checking storage conditions
- Enable and disable Swap (this feature can be used on devices with Linux OS)
- New UUID
- and others
You can use all of these features according to your needs. Using the features in GParted is not too difficult because the instructions are clear. Also, because GParted is GUI, it makes the instructions easy to understand.
How to Use GParted
- As usual, you download the GParted application.
- There will be an ISO file; then, you burn the file.
- Restart the computer and make sure that the boot CD-ROM is in the first place
- GParted is ready for you to use
- You can click Resize or Move if you want to adjust the size of the hard disk.
- You drag across the partition towards the left. Don’t forget to pay attention to the words New Size to create a new size and Free Space Following, the new partition you are using.
- Then you press the Resize or Move button to start this process
- You click the new partition in the Filesystem section. Then select ext3 and label ‘/.”
- Click the Add button, then apply to begin the partition change process.
- Restart the computer and see the size of the partition on the hard drive now
- Don’t forget to backup your data first before using GParted.
For your information, several versions of the Linux operating system that can use GParted include Fedora, Ubuntu, Debian, and Open Suse. GParted stands for Gnome Partition Editor, an application with a GUI or Graphic User Interface.
This application is used for storage management, namely SSD or hard disk. Functions of GParted as found in the Partition Wizard in DLC Boot for Windows OS. At the beginning of its creation, this application was intended for Linux OS.
However, now you can download GParted and use it for Windows OS. By using this application, you can edit, resize, or create or delete partitions on the storage media on your computer or laptop.
-

 Phones5 years ago
Phones5 years agoApple iPhone 11 (2019) – Release, Info, Leaks, Rumors
-
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-400x240.png)
![Huawei's New Operating System is HarmonyOS [ Officially ],harmony os,huawei new operating system, huawei harmony OS,](https://www.thedigitnews.com/wp-content/uploads/2019/08/Screenshot__2285_-removebg-preview-2-1-80x80.png) Phones5 years ago
Phones5 years agoHuawei New Operating System is HarmonyOS [ Officially ]
-

 News5 years ago
News5 years agoBelle Delphine bath water – Instagram Model Sells Used Bathwater For 30$ To Their Loyal Followers
-

 Tech5 years ago
Tech5 years agoLevi’s Bluetooth Jacket Lets You Control Your Smartphone